The word ‘open’ in a connected world can be something positive. Open source, for example, or open library. On other occasions the opposite can be true; unnecessary ports left open on a router springs to mind.
The word ‘open’ in a connected world can be something positive. Open source, for example, or open library. On other occasions the opposite can be true; unnecessary ports left open on a router springs to mind.
For millions of people using devices that appear to configure themselves, whether something is open or closed is irrelevant. If a device immediately works as promised, oftentimes that’s good enough. The problem with some internet-connected devices is that in order to immediately work in the hands of a novice, security gives way to ease of use, and that can end in disaster.
Torrent Client WebUI
Many of today’s torrent clients can be operated via a web interface, commonly known as a WebUI. A typical WebUI is accessed via a web browser, with the client’s IP address and a specified port number providing remote access.
In a LAN environment (the part of a network behind the router, such as a home) the torrent client’s web interface serves local users, i.e those with direct access to the local network, typically via Wifi. The problems begin when a torrent client’s WebUI is exposed to the wider internet. In broad terms, instead of the client being restricted to IP addresses reserved for local uses (starting 192.168.0.0 or 10.0.0.0), anyone with a web browser anywhere in the world can access the UI too.
In many cases, a WebUI can be secured with a password or by other means but when users are allowed to do that themselves, many never do, despite the warnings. That could end in disaster if the wrong person decides to let rip from the other side of the world.
Specialized Search Engines
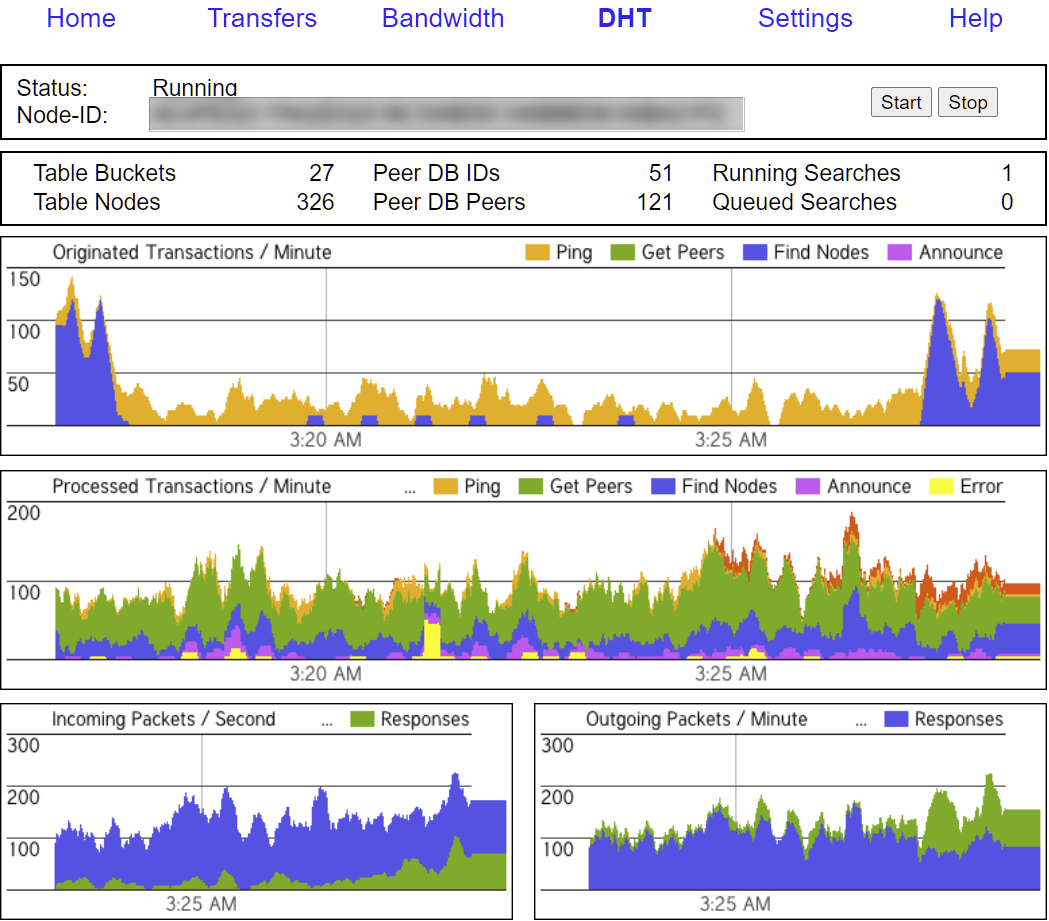
Internet-connected devices are easily found using services such as Shodan, Censys, Fofa and Onyphe.io and those that are poorly configured are in plentiful supply.
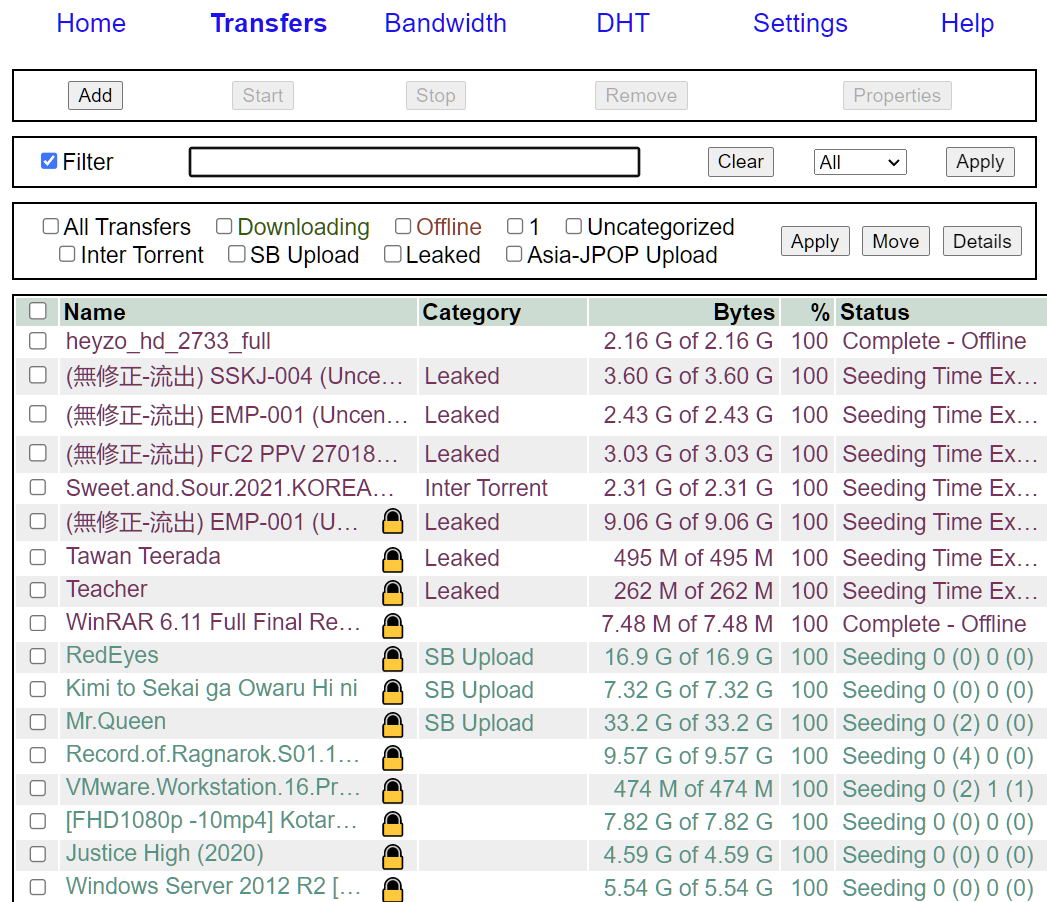
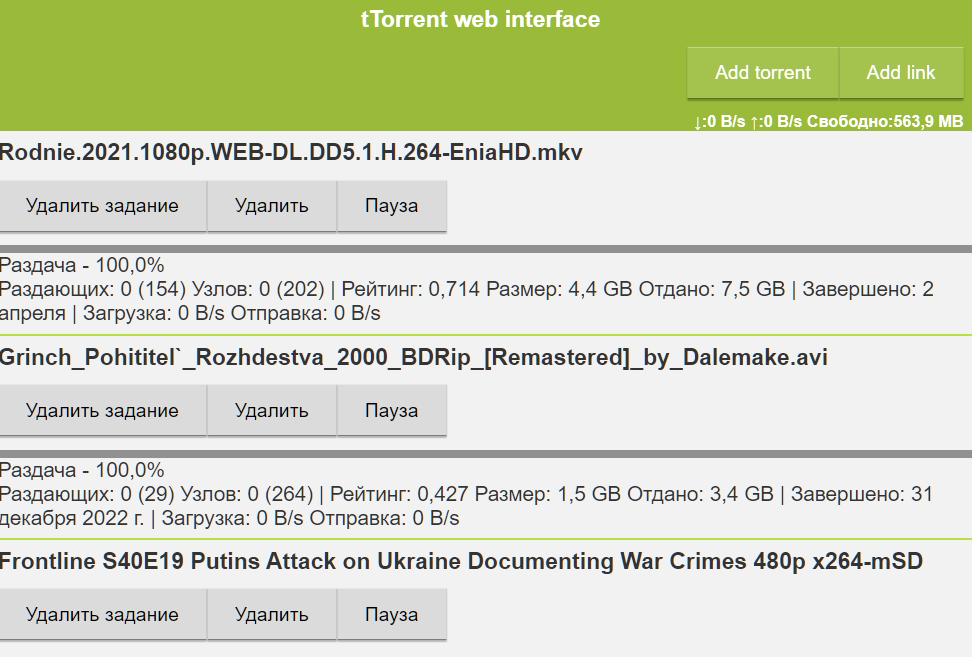
The image above shows a WebUI for the Tixati torrent client. With zero security, everything is on full display, just as it is for the person who operates the client, whoever they might be. This means that all downloads and uploads can be browsed, including data related to those transfers, as seen below.
It can take just a couple of minutes to find hundreds of open clients. A common WebUI seen in the wild belongs to qBittorrent but the overwhelming majority are locked down, just as they should be.
That’s Not Ideal
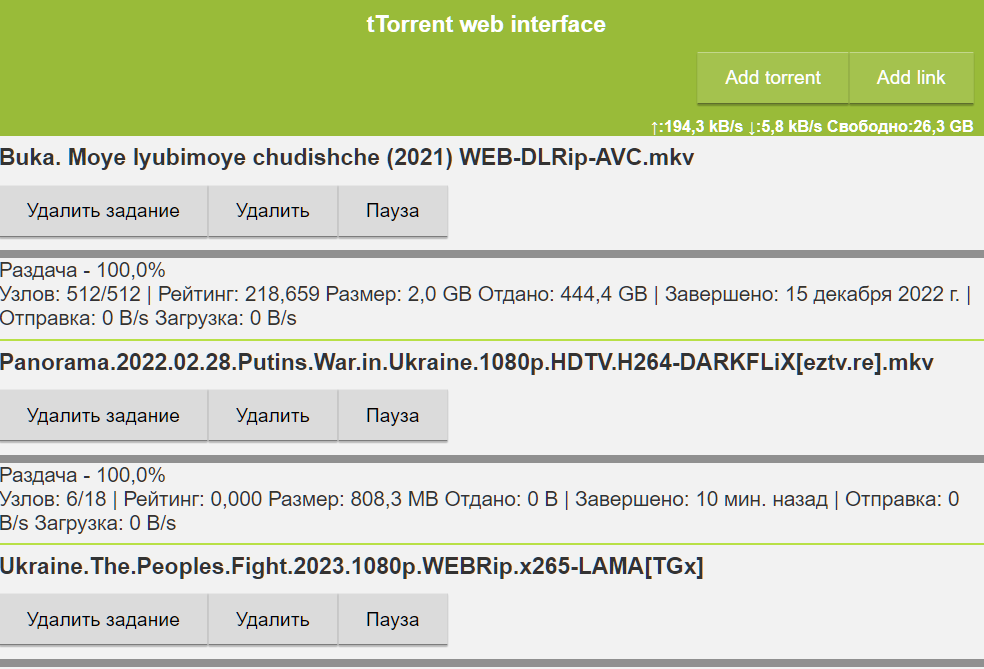
For reasons that aren’t entirely clear, the Android torrent client ‘tTorrent‘ is quite popular in Russia.

It’s possible that people install tTorrent on always-on set-top boxes, so the latest movies are ready to go as soon as they get home from work, or the local bar. The problem here is that with an entirely exposed WebUI, people can find out what Russians are downloading.

The average Russian citizen probably won’t mind if outsiders discover their Mortal Kombat habit; they made the decision to download it, so that’s that.
But what if strangers passing by in the night had influence over content consumed locally? What if those strangers decided to utilize their control of an open WebUI to share news from the other side of the world, downloaded directly to their new friend’s Android device?
If they did, it might look a lot like this….