 Last month, researchers at IT security company ESET reported on a new type of OS X malware. Called OSX/Keydnap, the malicious software was designed to steal the content of OS X’s keychain while inserting a backdoor.
Last month, researchers at IT security company ESET reported on a new type of OS X malware. Called OSX/Keydnap, the malicious software was designed to steal the content of OS X’s keychain while inserting a backdoor.
In a detailed blog post on the topic, ESET said that it was unclear how machines became infected with OSX/Keydnap but speculated that it might be through attack vectors such as spam, downloads from untrusted websites, “or something else”. Other things were certain, however.
“What we know is that a downloader component is distributed in a .zip file. The archive file contains a Mach-O executable file with an extension that looks benign, such as .txt or .jpg. However, the file extension actually contains a space character at the end, which means double-clicking the file in Finder will launch it in Terminal and not Preview or TextEdit,” the researchers wrote.

Now, several weeks later, it now transpires that some BitTorrent users have been exposed to OSX/Keydnap. While some might presume that could have taken place through a suspect download from an infected torrent (also possible), this particular attack actually took place from a trusted source.
ESET reports that a recompiled version of the open source BitTorrent client Transmission was offered for download on the software’s official website. Somehow, that software had already become infected with OSX/Keydnap. Once informed, the Transmission team were quick to act.
“Literally minutes after being notified by ESET, the Transmission team removed the malicious file from their web server and launched an investigation to identify how this happened,” the researchers explain.
“According to the signature, the application bundle was signed on August 28th, 2016, but it seems to have been distributed only the next day.”
Following an investigation by the Transmission team, we now know how the infected version came to be offered to the public and for how long. It all began with some kind of intrusion by an as-yet-unamed attacker.
“It appears that on or about August 28, 2016, unauthorized access was gained to our website server,” the team said in a statement.
“The official Mac version of Transmission 2.92 was replaced with an unauthorized version that contained the OSX/Keydnap malware. The infected file was available for download somewhere between a few hours and less than a day.”
The team says that they infected file was removed from the server immediately upon its discovery, potentially just a few hours after it was placed there. While any period is too long, the length of time the download was made available to the public should help to limit the impact of the malware.
For anyone concerned that they still might have been infected during that period, ESET offers the following advice to check for infection.
“We advise anyone who downloaded Transmission v2.92 between August 28th and August 29th, 2016, inclusively, to verify if their system is compromised by testing the presence of any of the following file or directory,” the company writes.
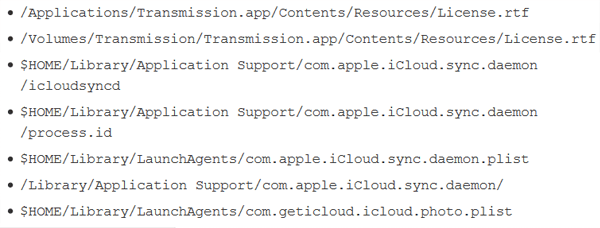
“If any of them exists, it means the malicious Transmission application was executed and that Keydnap is most likely running. Also note that the malicious disk image was named Transmission2.92.dmg while the legitimate one is Transmission-2.92.dmg (notice the hyphen).”
The Transmission team has also published a detailed guide for anyone concerned about infection. They’re also taking additional steps to limit the chances of this happening again.
“To help prevent future incidents, we have migrated the website and all binary files from our current servers to GitHub. Other services, which are currently unavailable, will be migrated to new servers in the coming days,” the team says.
“As an added precaution, we will be hosting the binaries and the website (including checksums) in two separate repositories.”
Uninfected versions of Transmission can be downloaded here. Versions for operating systems other than OS X are not affected.









