 Little over two weeks ago we broke the news that a user, going by the name “Widevinedump”, had leaked a collection of movie ripping scripts on GitHub.
Little over two weeks ago we broke the news that a user, going by the name “Widevinedump”, had leaked a collection of movie ripping scripts on GitHub.
These were high-profile leaks as Widevine is one of the leading content protection tools in the video business. The Google-owned technology is used by many of the largest streaming services including Amazon, Netflix and Disney+.
The code allows people to download HD video from popular streaming platforms including Disney+, Amazon, and Netflix. And indeed, soon after the repositories were live, sources confirmed that it was doing just that.
The person who posted the code didn’t necessarily create it. Most of these tools were already circulating elsewhere, often in private groups. However, by appearing on GitHub they became more public than ever before.
MPA Asks GitHub to Remove the Scripts
In our initial report, we mentioned that rightsholders would likely take swift action in response. That was indeed the case, as the Motion Picture Association sent a takedown notice to GitHub on December 31, which was made public by GitHub a few hours ago.
“Widevine is proprietary software that prevents stream ripping, and the scripts circumvent that by exploiting a vulnerability to allow stream ripping,” MPA wrote in its initial takedown notice.
Acting on behalf of its members, including Disney and Netflix, MPA requested GitHub to remove the “Widevinedump” repositories including ‘DISNEY-4K-SCRIPT’, ‘Netflix-4K-Script’, ‘WV-AMZN-4K-RIPPER’, ‘APPLE-TV-4K-Downloader’ and several others.
“In short, the poster has written scripts to circumvent DRM on multiple streaming platforms, including Disney+, Amazon Prime, Netflix, and others. These scripts allow users to rip (download) streams directly to their devices, and, then, distribute them on the internet,” MPA told GitHub.
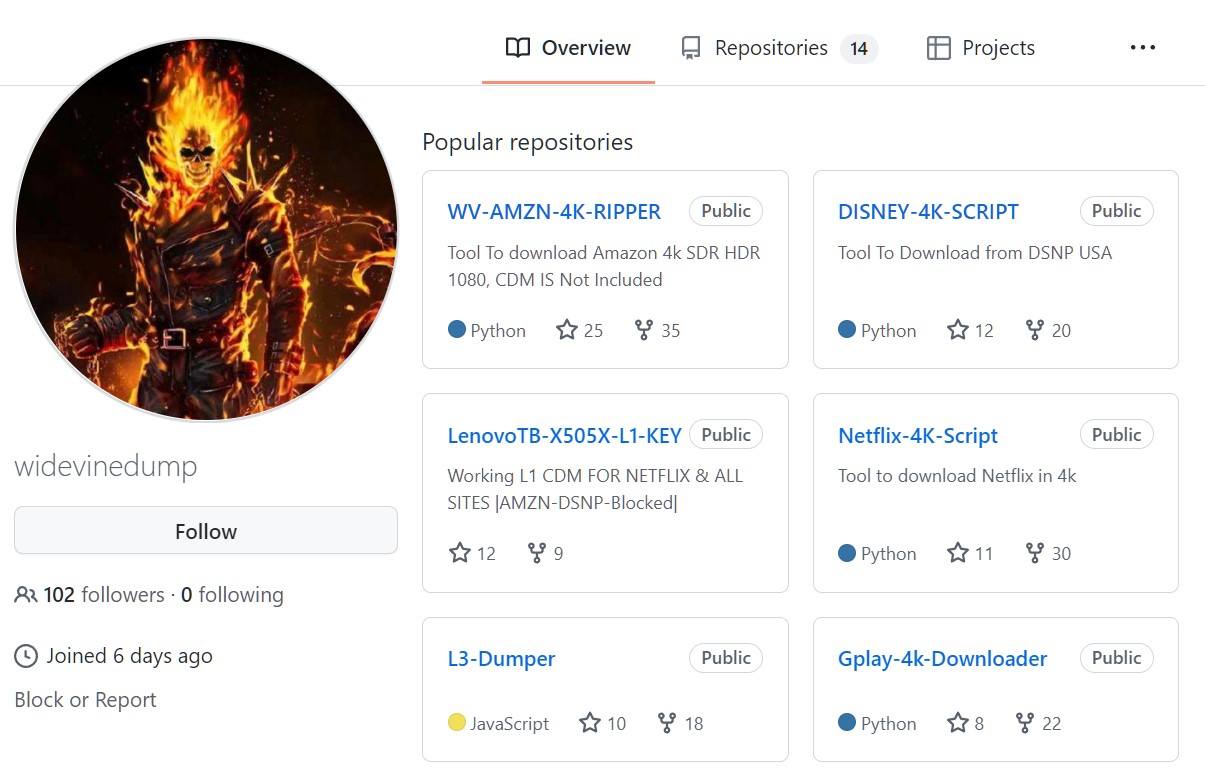
Around the same time that the MPA sent its notice, these repositories indeed went offline. However, it is unclear whether GitHub took action. When the platform makes a repository unavailable it will generally display an “unavailable due to DMCA takedown” notice. The Widevinedump links, however, return a 404 error and the account itself has been deleted.
Before the MPA sent its takedown notice, “Widevinedump” already informed us that the code would be removed voluntarily in a few days. Perhaps the MPA’s takedown notice was the final nudge?
Hundreds of Forks Appeared
With the repositories offline, the problem wasn’t fully resolved. During the first few days after the leak appeared, hundreds of forks showed up as well, which (partially) copied the code.
To deal with this aftermath, the MPA sent another takedown notice last week, which was also made public a few hours ago. This request lists hundreds of forks that allegedly include the same code.
“The [Widevinedump] scripts have been removed and we have also reviewed the fork network to determine those that contain the content we reported as a violation of the DMCA in the parent repository,” MPA writes.
The notice itself lists hundreds of links. We tried to access these today and found that some point to a 404 error, while others list a DMCA takedown message, as shown below.

Responding to MPA’s notice, GitHub says that it applied the request to the entire network of forks, which includes 934 repositories. However, a quick search of the platform reveals that some copies are still floating around, so this may not be the end of the matter.
When “Widevinedump” posted the scripts they wrote that it was a retaliatory move against some people in a Discord group. These people may have returned fire, as the alleged leaker was doxed a few days later.
Finally, it is worth noting that “Widevinedump” asked for money in return for working Content Decryption Modules (CDMs), which are required to use most scripts. Whether people actually paid for and received these CDMs is unknown but that could obviously lead to all sorts of disappointments and even legal trouble.









