 Dated April 2012, the IFPI report obtained by TorrentFreak was put together by the music industry group’s chief anti-piracy officer Mo Ali.
Dated April 2012, the IFPI report obtained by TorrentFreak was put together by the music industry group’s chief anti-piracy officer Mo Ali.
The 30-page report presents a global view of IFPI’s “problems”, “current and future threats” and the industry’s responses to them.
IFPI says it has five possible reactions to a threat: Take down, Disruption, Investigation, Lobbying and Litigation.
The Threats: P2P
Initially IFPI splits illicit content availability into two sections. The first they classify as “content held on users’ computers” and distributed via P2P networks such as BitTorrent, Gnutella, DirectConnect, eDonkey and Ares.
It says it has taken “strategic action” against The Pirate Bay (BitTorrent), LimeWire (Gnutella) and also the semi-private tracker Demonoid (BitTorrent). IFPI doesn’t elaborate on action against the latter, but it was rumored that a member of the site’s staff was targeted a while back.
Central hosting/cyberlockers
The second category is content held on central servers, including file-hosts and cyberlockers. Interestingly, the IFPI diagram below shows that when the group examined allegedly infringing URLs on the world’s major cyberlockers, Megaupload’s stats paled into insignificance when compared to the others.

IFPI is clear on their requirements for cyberlockers to operate to their liking. Their number one desire is that they “proactively filter for infringing content” but if they don’t they must “operate an effective and efficient notice and take down system.” Failure to implement either means sites will be required to “shut down”.
Hacking and phishing attacks
One of the other threats detailed by IFPI include hacking and phishing attacks against email accounts of artists and their management. Through these techniques individuals are apparently obtaining unauthorized access to pre-release music.
IFPI say a number of techniques are being used, from bogus emails claiming to be from social networking, email, or cyberlocker sites, to the compromising of password reset features. Once accessed, mail is forwarded to other accounts, either with the music attached or with valuable information which allows other systems to be accessed.
The rise of mobile data and applications
IFPI is also keeping a close eye on the downloading and sharing of content across mobile data and other wireless networks. IFPI worries that these networks are providing here-and-now streaming of content via all-you-can-eat plans. Making matters worse is that IFPI reports “challenges” when it comes to matching an IP address to a subscriber.
The recording group also reports that Apple and Android architectures are encouraging the creation of 3rd party music apps. IFPI say they are crawling both the App Store and Google Marketplace and are focusing on “quick take down agreements” with Apple, Google, Microsoft, Nokia and Palm to remove apps they don’t like. They are also mulling an expansion of their “payment provider program” to target “rogue” Android app developers.
Unauthorized pay MP3 sites
IFPI say they have identified in excess of 50 Russian and Ukrainian pay MP3 download sites. The group reports that law enforcement authorities have “secured evidence that the illegal sites are annually stealing hundreds of millions of dollars” which is creating opportunities for money laundering and tax evasion investigations. IFPI say their next steps will include strangling the sites’ finances with the help of payment processors, recovering proceeds of crime, and developing asset confiscation.
Advertisers and payment processors
IFPI’s advertiser strategy is based around the “disruption of revenue streams” to unauthorized sites by several methods. In the report they speak of a “structured notice and take down programme targeting Google’s AdSense and DoubleClick advertising networks,” plus “out reach” to IASH and IAB to implement “comprehensive infringing block lists.” IFPI says it also initiates direct contact with advertisers to flag when their ads appear on infringing sites.
Agreements are said to be in place with VISA, MasterCard, PayPal, CTIA, Monitise, PaySafeCard and PhonePayPlus to strangle finances to unauthorized sites.
Dealing with Internet service providers
In common with cyberlockers, IFPI have a set of rules they’d like to impose on Internet service providers. According to the industry group, ISPs should not provide Internet access to infringing sites, services or even unidentified customers. Furthermore, ISPs are required to “Implement a system of graduated response for infringing P2P users including warnings to an effective deterrent sanction.”
Site Blocking
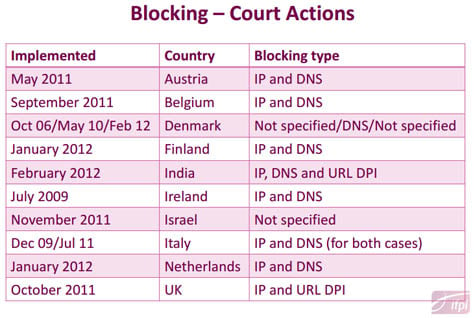
ISPs are also required by IFPI to block access to infringing sites and services “located outside the local jurisdiction.” The chart below shows where blocking orders have been obtained (prior to April 2012) and how they are carried out.
Surprisingly, despite reports mounting to the contrary, IFPI seems to think that site blocking is an almost perfect solution to counter infringement.
“The effectiveness of such a ‘block’ will depend on the determination of the ISP subscriber
and the content/website provider to maintain access to each other and to use circumvention techniques to bypass blocking techniques,” they write.
“There is evidence to suggest that there is limited (between 3% and 5%) adoption of these circumvention techniques although subscribers with more technical knowledge could look to circumvent ISP controls using virtual private networks (VPN) or anonymous proxies.”
Conclusions
IFPI finishes up by stressing the importance of “co-operation, partnerships and information exchange” and the building of relationships with law enforcement, judges and legal bodies in order to “provide training built around ‘real world’ experiences and challenges rather than focusing on theory.”

Amendments to relevant laws need to be planned for the future, but in the short term IFPI should “consider ‘quick, curve ball’ solutions to impact more complex operations as
complement to long term investigations,” the group concludes.









