Earlier this year WikiLeaks, the world’s largest whistleblower website that allows people to publish uncensored information anonymously, suspended its operations due to problems with funding. Through donations, by February 6th it had achieved its minimum funding-raising goal and was eventually restored to its former glory.
Although rarely out of the news for long, on 5th April 2010 WikiLeaks grabbed headlines worldwide after releasing a classified US military video “depicting the indiscriminate slaying of over a dozen people in the Iraqi suburb of New Baghdad — including two Reuters news staff.”
Yesterday the site was in the spotlight again, after ex-hacker Adrian Lamo (who TorrentFreak spoke with recently about a movie leak) admitted that he had informed the authorities who had leaked the so-called “Collateral Murder” video to WikiLeaks.
Of course, all this attention leads to big bills for WikiLeaks as it continues to fund the distribution of leaked documents to the world. Thus far it has carried that out from its own servers but recently it has made a rather interesting addition to its system.
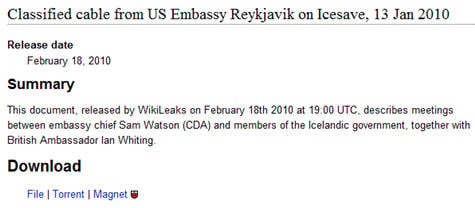
In the ‘Download’ section for individual documents, in addition to the usual direct link ‘FILE’ (.zip) download, two other buttons have been added – ‘Torrent’ and ‘Magnet’.
These files are smaller than the most of the documents hosted on WikiLeaks and allow readers to download the material from BitTorrent users around the world, utilizing their bandwidth rather than the site’s.
However, regardless of where the material is stored people will still need to download the .torrent or magnet links in order to access the material. This would continue to be a problem if WikiLeaks went down due to funding or other more serious problems, such as an attack from a hostile government. Hosting these links in other places would therefore seem to be a good idea. But what if there was another hybrid-style option?
“What if WikiLeaks was a sort of Wiki-BitTorrent, served by thousands of people around the world running a background process on their computers,” mused Edward Benson, a Ph.D. student at the MIT Computer Science and Artificial Intelligence Laboratory.
“No fundraising needed here, it’s all P2P. And if the Wiki is maintained WikiPedia style, then we no longer need to pay for a centralized staff to curate it. Plus, there’s no centralized staff to kill or jail. It can be a decentralized, collaborative process,” Benson noted back in March, before WikiLeaks started added .torrent and magnet links.
However, a full Wiki-BitTorrent type system has its problems. Without public confidence in the publisher of this leaked information – in this case the established reputation of WikiLeaks – how can anyone be certain that the information they’re getting from a BitTorrent-type system is actually what it says it is?
“If WikiLeaks was P2P, then it could be attacked — poisoned at the infrastructural level by the governments and corporations that do not want to see it succeed. Even worse, a P2P WikiLeaks could be left standing, but its content could be poisoned with fake and misleading files,” adds Benson.
Most readers will be familiar will the concept of the fake or useless download. From the spoofed files uploaded by the RIAA onto shared-folder type file-sharing networks containing nothing but silence or other useless junk, to the malware, renamed or otherwise manipulated files of uncertain origin of today. With a music or video file this is a minor inconvenience, for a leaked document of global significance and implications, errors or deliberately misleading information would be an unmitigated disaster. It is here that Benson notes an irony in his analysis of WikiLeaks.
“What if this experiment in citizen’s power is successful precisely because it is a dictatorship?”
As with the ‘verified downloads’ offered by many torrent sites today, it seems that at least for now there is a requirement for a central source of trust to ensure that the material being offered is what it says it is, whether it’s the recreational business of grabbing media or the world-changing implications of leaked documents.









