 In recent years, software applications that provide access to the latest movies, TV shows, live TV and premium sports events have become increasingly popular.
In recent years, software applications that provide access to the latest movies, TV shows, live TV and premium sports events have become increasingly popular.
Most commonly available for Android, PC, and iOS platforms, these tools often come pre-configured for piracy meaning that when they installed, the latest content is just a few clicks away. This approach means that such apps can be quickly ejected from Apple’s App Store and Google Play on the basis they are self-contained piracy tools. However, there is another way.
Evading App Store and Google Play Removal
Exposure on official app stores is a tried-and-tested method to grow public awareness of an app but if they are quickly removed for infringement, that all falls apart. To prevent this from happening, apps have been appearing on both platforms that are capable of supplying infringing content but have crucial components missing at the point of download. These need to be added in at a later point to provide functionality.
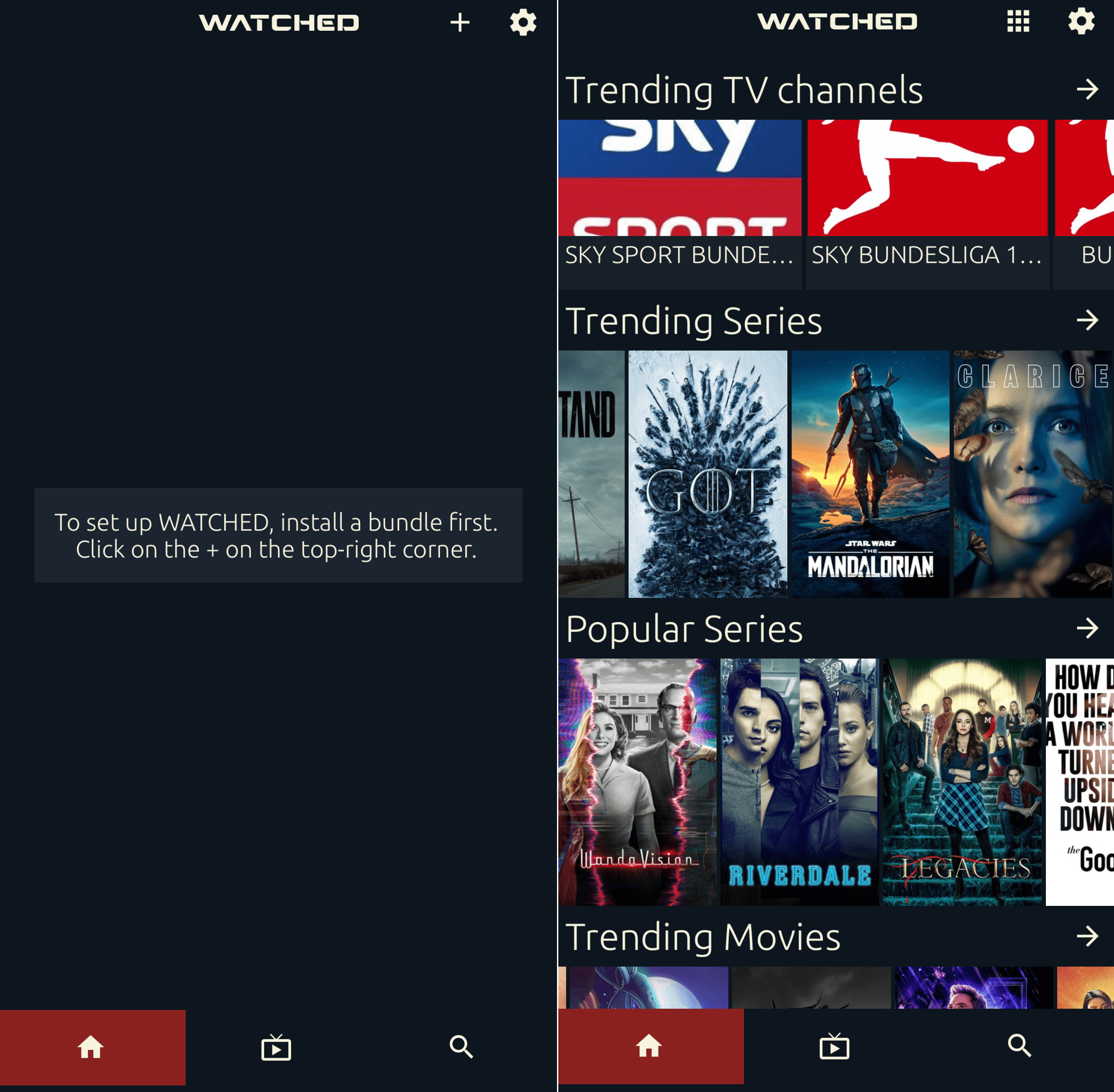
One example is the ‘Watched‘ streaming app which at the time of writing is in the Top 30 most popular entertainment apps on Apple’s App Store. No content is presented in the app but after installation, users are prompted to supply a ‘bundle’ via a URL of their choosing. No information is provided as to what this URL should be but a little searching online reveals that certain URLs make ‘Watched’ much more useful.
‘Watched’ Bundle Available at Oha.to
One of the more popular ‘bundle’ URLs is Oha.to and when this is entered into ‘Watched’ it transforms the app in much the same way as adding a third-party repository/addon to Kodi might. The website at this URL contains the necessary components to fill ‘Watched’ with movies, TV shows and live TV channels, which are all accessible via the provided interface.
While the ‘Watched’ app remains accessible on app stores and via the software’s homepage, there are moves by global entertainment industry companies to target bundle URLs, including Oha.to.
ACE Goes to Court in the United States
The Alliance For Creativity and Entertainment (ACE) is a global anti-piracy coalition that brings together dozens of the most powerful entertainment industry companies in the world. These include the major Hollywood studios plus Netflix and Amazon, all of which aim to disrupt the illegal streaming market to protect their businesses.
Yesterday, ACE members filed an application for a DMCA subpoena against Cloudflare in a California court and the complaint itself shows how convoluted these matters can become.
Cloudflare provides services to Oha.to but at least as far as we can tell (and like Cloudflare), Oha.to doesn’t carry any infringing content either. Instead, Oha.to provides a service that enables end-users of ‘Watched’ to find content to which ACE members hold the rights.
“We have determined that individuals operating and controlling Oha.to have infringed ACE Members’ Copyrighted Works by using Cloudflare servers, networks, and other services, to connect end users of the ‘Watched’ mobile application to websites containing infringing content,” explains MPA Executive Vice President & Chief of Global Content Protection, Jan van Hoorn.
“The Oha.to service receives requests for infringing content from the Watched application, scrapes various links to identify cyberlockers containing the requested infringing content, and returns a response containing the scraped links to the application, which allows users of the Watched application to stream infringing content.”
ACE Wants To Unmask The Operator(s) Of Oha.to
The purpose of the ACE legal action is to find out who is behind the Oha.to repository/bundle. In common with similar requests, it requires Cloudflare to hand over the personal identities of the people behind the website, including their names, physical addresses, IP addresses, telephone numbers, email addresses, payment information and account histories.
Whether Cloudflare will have any useful information to hand over is unclear but this is not the first time that ACE has gone after component services that allow ‘Watched’ to function.
As reported last November, ACE previously filed an application for a similar DMCA subpoena against the Tonic domain registry in an effort to discover the identities of the individuals behind Huhu.to.
This domain operates in a similar if not identical manner to Oha.to, in that people who use the ‘Watched’ app can enter the domain when prompted to supply a ‘bundle’ URL, prompting the ‘Watched’ app to do something useful. It’s unknown whether Tonic was able to provide any useful information in this case but the domain is fully functional at the time of writing.
The ACE application for DMCA subpoena can be found here (1,2)









