 The beauty of BitTorrent is that thousands of people can share a single file simultaneously to speed up downloading. In order for this to work, trackers announce the IP-addresses of all file-sharers in public.
The beauty of BitTorrent is that thousands of people can share a single file simultaneously to speed up downloading. In order for this to work, trackers announce the IP-addresses of all file-sharers in public.
The downside of this approach is that anyone can see who’s sharing a particular file. It’s not even required for monitoring outfits to actively participate.
This ‘vulnerability’ is used by dozens of tracking companies around the world, some of which send file-sharers warning letters, or worse. However, the “spies” are not just getting info from trackers, they also use BitTorrent’s DHT.
Through DHT, BitTorrent users share IP-addresses with other peers. Thus far, little was known about the volume of monitoring through DHT, but research from Peersm’s Aymeric Vitte shows that it’s rampant.
Through various experiments Vitte consistently ran into hundreds of thousands of IP-addresses that show clear signs of spying behavior.
The spies are not hard to find and many monitor pretty much all torrents hashes they can find. Blocking them is not straightforward though, as they frequently rotate IP-addresses and pollute swarms.
“The spies are organized to monitor automatically whatever exists in the BitTorrent network, they are easy to find but difficult to follow since they might change their IP addresses and are polluting the DHT with existing peers not related to monitoring activities,” Vitte writes.
The research further found that not all spies are actively monitoring BitTorrent transfers. Vitte makes a distinction between level 1 and level 2 spies, for example.
The first group is the largest and spreads IP-addresses of random peers and the more dangerous level 2 spies, which are used to connect file-sharers to the latter group. They respond automatically, and even return peers for torrents that don’t exist.
The level 2 spies are the data collectors, some if which use quickly changing IP-addresses. They pretend to offer a certain file and wait for BitTorrent users to connect to them.
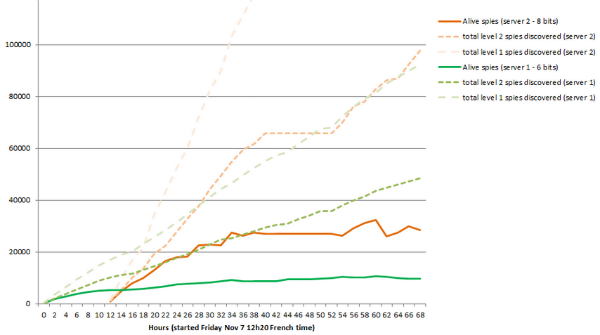
The image below shows how rapidly the spies were discovered in one of the experiments and how quickly they rotate IP-addresses.
Interestingly, only very few of the level 2 spies actually accept data from an alleged pirate, meaning that most can’t proof without a doubt that pirates really shared something (e.g. they could just be checking a torrent without downloading).
According to Vitte, this could be used by accused pirates as a defense.
“That’s why people who receive settlement demands while using only DHT should challenge this, and ask precisely what proves that they downloaded a file,” he says.
After months of research and several experiments Vitte found that there are roughly 3,000 dangerous spies. These include known anti-piracy outfits such as Trident Media Guard, but also unnamed spies that use rotating third party IPs so they are harder to track.
Since many monitoring outfits constantly change their IP-addresses, static blocklists are useless. At TF we are no fans of blocklists in general, but Vitte believes that the dynamic blocklist he has developed provides decent protection, with near instant updates.
This (paid) blocklist is part of the Open Source Torrent-Live client which has several built in optimizations to prevent people from monitoring downloads. People can also use it to built and maintain a custom blocklist.
In his research paper Vitte further proposes several changes to the BitTorrent protocol which aim to make it harder to spy on users. He hopes other developers will pick this up to protect users from excessive monitoring.
Another option to stop the monitoring is to use an anonymous VPN service or proxy, which hides ones actual IP-address.









