 Ever since the launch of Apple’s app-enabled devices, users have sought ways to run software not sourced from the official App Store. It’s been a cat-and-mouse battle, with teams of security experts trying to break Apple’s security to enable a process known as ‘jailbreaking’.
Ever since the launch of Apple’s app-enabled devices, users have sought ways to run software not sourced from the official App Store. It’s been a cat-and-mouse battle, with teams of security experts trying to break Apple’s security to enable a process known as ‘jailbreaking’.
A successfully jailbroken iPhone, for example, can not only run software from third party app stores such as Cydia, but can also run pirated iOS software. Needless to say, with this feature the popularity of jailbreaking has soared, prompting Apple to do everything it can to close security holes.
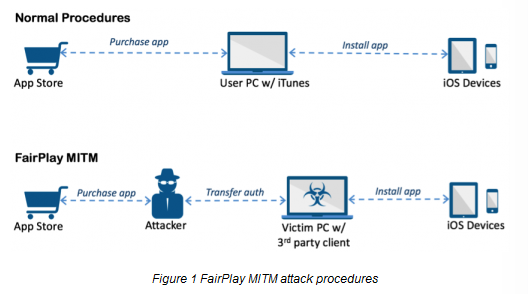
However, in 2013 something unexpected happened. A new technique known as the “FairPlay Man-In-The-Middle” (MITM) attack exploited flaws in Apple’s ‘Fairplay’ DRM system to allow both pirated and third-party software (unapproved by Apple) to run on iOS devices. Crucially, this could all take place without a jailbreak being deployed on the device.
Somewhat surprisingly people with the ability to carry out the third-party software exploit have been remarkably well behaved for the past three years but all good things come to an end. Rather than using the loophole for consumer-friendly activity, attackers are now using it for evil.
According to Palo Alto Networks researcher Claud Xiao, there now exists iOS malware that is able to deploy itself to non-jailbroken devices using the man-in-the-middle attack previously used by pirates.
Named “AceDeceiver” by the researcher, the malware targets the method of transferring App Store purchases from the iTunes software installed on users’ computers to their iOS devices.
“iOS devices will request an authorization code for each app installed to prove the app was actually purchased,” Xiao explains.
“In the FairPlay MITM attack, attackers purchase an app from App Store then intercept and save the authorization code. They then developed PC software that simulates the iTunes client behaviors, and tricks iOS devices to believe the app was purchased by victim. Therefore, the user can install apps they never actually paid for, and the creator of the software can install potentially malicious apps without the user’s knowledge.”
But to do its dirty deeds AceDeceiver needs to find a way onto a user’s device in the first instance and that was achieved via Apple’s very own App Store.
Between July 2015 and February 2016 software claiming to be wallpaper apps successfully passed Apple’s vetting systems and were made available to Apple users. The way this was achieved was extremely cunning, with the App only going into malicious mode if it was run in a certain geographical area, in this case, China.
“The iOS apps of AceDeceiver mainly act as a third party app store if users access them from China. Note that some of the apps or games they provide in the store are also installed through a FairPlay MITM attack. In addition, these apps strongly suggest users input their Apple ID with password so that users could ‘directly install free apps from the App Store, execute in-app purchase, and login to Game Center’.”
That doesn’t sound like good news and indeed, the researchers found that claims that the software did not transfer login credentials were simply untrue.
“In fact, we discovered all versions of AceDeceiver will upload the Apple ID and password to [the attackers’ server],” Xiao adds.
All three apps were removed by Apple after the researchers reported them in February 2016 but their threat remains.
“The attack is still viable because the FairPlay MITM attack only requires these apps to have been available in the App Store once. As long as an attacker could get a copy of authorization from Apple, the attack doesn’t require current App Store availability to spread those apps,” Xiao explains.
“While the attack requires a user’s PC to be infected by malware first, after that, the infection of iOS devices is completed in the background without the user’s awareness. The only indication is that the new malicious app does appear as an icon in the user’s home screen, so the user may notice a new app he or she won’t recall downloading.”
The full disclosure from Claud Xiao can be found here, along with removal instructions for those concerned they may be infected by the malware.









