 In recent years we have documented a wide range of patent applications, several of which had a clear anti-piracy angle.
In recent years we have documented a wide range of patent applications, several of which had a clear anti-piracy angle.
Symantec Corporation, known for the popular anti-virus software Norton Security, is taking a more torrent-friendly approach. At least, that’s what a recently obtained patent suggests.
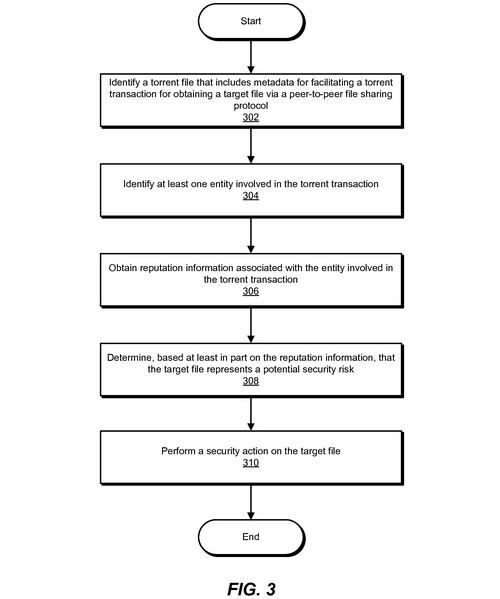
The patent describes a system that can be used to identify fake torrents and malware-infected downloads, which are a common problem on badly-moderated torrent sites. Downloaders of these torrents are often redirected to scam websites or lured into installing malware.
Here’s where Symantec comes in with their automatic torrent moderating solution. Last week the company obtained a patent for a system that can rate the trustworthiness of torrents and block suspicious content to protect users.
“While the BitTorrent protocol represents a popular method for distributing files, this protocol also represents a common means for distributing malicious software. Unfortunately, torrent hosting sites generally fail to provide sufficient information to reliably predict whether such files are trustworthy,” the patent reads.
Unlike traditional virus scans, where the file itself is scanned for malicious traits, the patented technology uses a reputation score to make the evaluation.
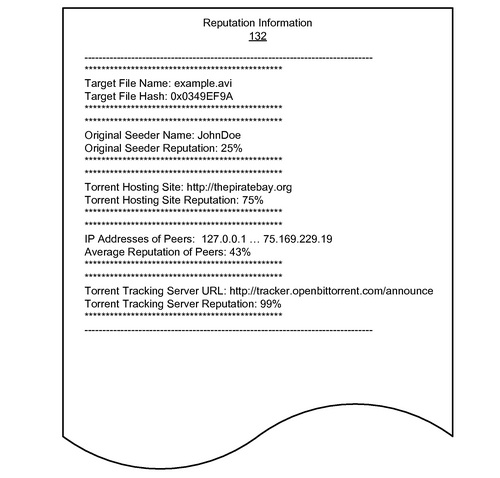
The trustworthiness of torrents is determined by factors including the reputation of the original uploaders, torrent sites, trackers and other peers. For example, if an IP-address of a seeder is linked to several malicious torrents, it will get a low reputation score.
“For example, if an entity has been involved in several torrent transactions that involved malware-infected target files, the reputation information associated with the entity may indicate that the entity has a poor reputation, indicating a high likelihood that the target file represents a potential security risk,” Symantec notes.
In contrast, if a torrent is seeded by a user that only shares non-malicious files, the trustworthiness factor goes up.
If a torrent file has a high likelihood of being linked to malware or other malicious content, the system can take appropriate “security actions.” This may be as simple as deleting the suspicious torrent, or a more complex respone such as blocking all related network traffic.
“Examples of such security actions include, without limitation, alerting a user of the potential security risk, blocking access to the target file until overridden by the user, blocking network traffic associated with the torrent transaction, quarantining the target file, and/or deleting the target file,” Symantec writes.
Symantec Corporation applied for the pattern nearly four years ago, but thus far we haven’t seen it used in the real world.
Many torrent users would likely appreciate an extra layer of security, although they might be concerned about overblocking and possible monitoring of their download habits. This means that, for now, they will have to rely on site moderators, and most importantly, common sense.









